Relieve IT’s Concerns With This New, More Secure Way to View Video Remotely
No NVR Port Forwarding Required
Filed under: Hybrid NVRs, Cybersecurity
Viewing video surveillance remotely is an important security requirement for most businesses, but lately, this need for remote access is coming into conflict with IT policies that aim to limit network exposure to the Internet.
Specifically, increased cybersecurity rules have IT departments clamping down on the practice of port forwarding, the typical method used to access a network video recorder (NVR) over the Internet.
In most IP video surveillance networks, a business network’s firewall is configured to allow inbound connections to the NVR. For example, if I want to login from home to see the surveillance cameras installed in my store, I need to communicate with my NVR. In order to do this, I must know the NVR’s public IP address as well as the “ports” it uses to communicate. Those ports must be open on my business firewall and forwarded to my NVR, so I can have access.
Remote video surveillance access with port forwarding
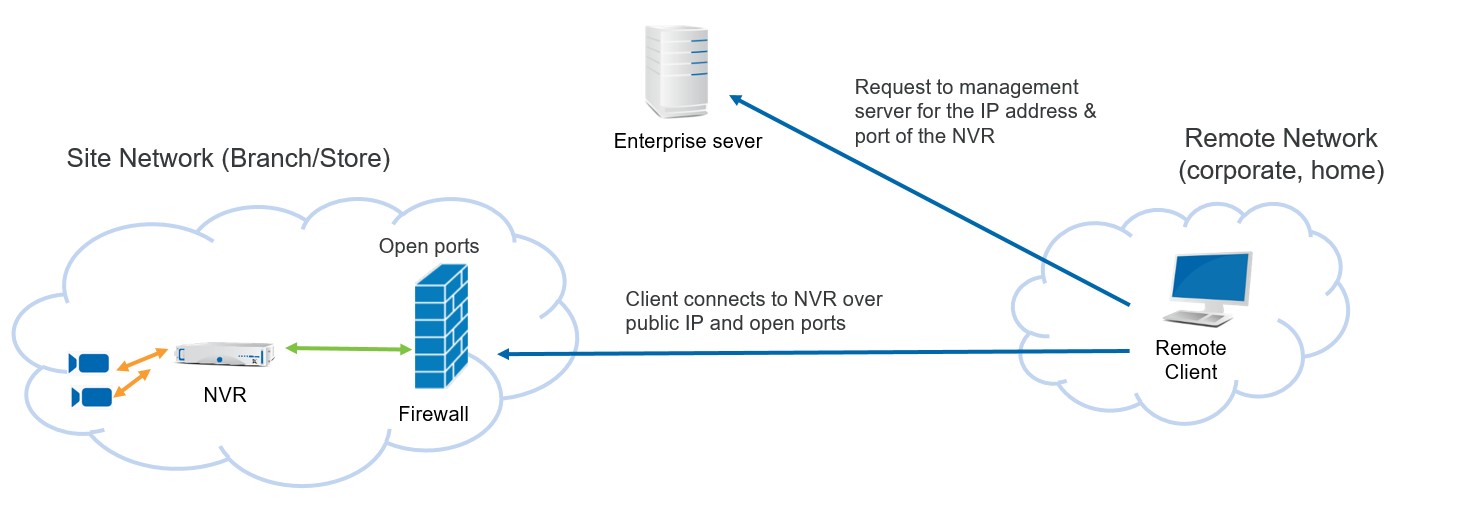
The flipside of this, however, is that these open ports expose the NVR to the Internet, potentially making it more vulnerable to cyberattack. This, obviously, does not sit well with many IT departments, who are tasked with reducing exposure to cyber threats and closing every possible loophole.
That’s why some video manufacturers including March Networks are adopting a new networking method known as Network Address Translator (NAT) traversal.
In video surveillance applications, NAT traversal allows users to connect to their recorders securely from any location without a VPN, direct connectivity, or the need for port forwarding. It does this by establishing direct, peer-to-peer (P2P) communications between the client device (your smartphone, tablet or home computer) and your recorder.
With NAT traversal, the communication is outbound from the NVR to the management server, so it never exposes the NVR to the Internet without a secure, authenticated connection.
So when I want to use my home computer or tablet to see my business surveillance, I make the request and if my NVR is registered to the March Networks Command Enterprise Server, I can access the video through NAT traversal.
Remote video surveillance access with NAT Traversal
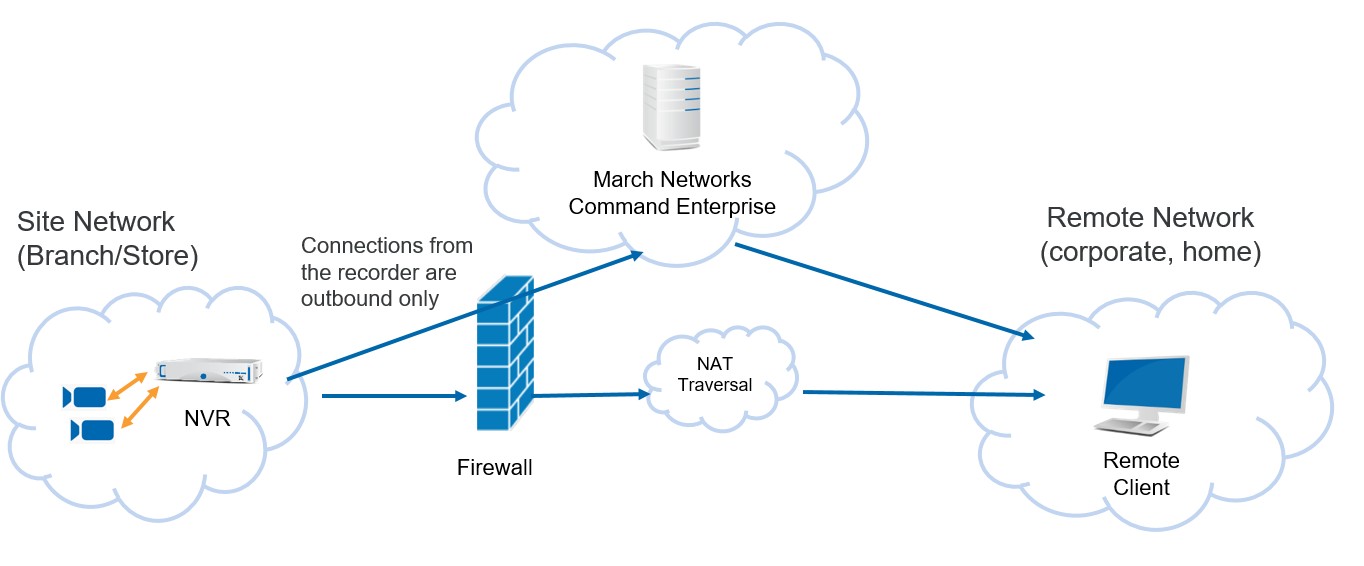
I like to think of it as a separate, private highway for my video and data communications. The communication remains secure because March Networks Command Enterprise acts as a gatekeeper, and only allows those with Command authorizations to pass through.
In other words, you can’t drive on the private highway unless you’ve been invited.
It’s a more secure way to view video remotely; all communications between the NVRs and Command are controlled and March Networks’ video and data transport is fully encrypted.
In addition to that, NAT traversal also uses encryption, making this an inherently secure way to view video remotely.
You can take advantage of this new capability by upgrading to March Networks latest recorder, mobile app and enterprise software releases. Talk to your March Networks sales representative to learn more or post a question or comment below:
Comments
Joe
Nice infol