No VPN? No Problem: An Alternative for Granting Access to Your Network for Remote Video Monitoring
Filed under: Cybersecurity
In today’s business world, many organizations rely on third-party vendors to provide critical services and support via the cloud. Often, this entails granting vendors remote access to your internal network so they can perform their services. Given cybersecurity concerns – such as data breaches, phishing, malware, and ransomware attacks – granting remote access to a third party can be unnerving for some, especially those who have experienced a network breach in the past. When it comes to remote monitoring of your on-premises video assets, it’s reassuring to know there are a couple of methods of granting network access to your provider.
With a remote video monitoring service, the health management of your network video recorders (NVRs) and IP cameras is handled remotely by a third-party provider, usually as a subscription-based service. This can help your organization save time and free up valuable resources.
In the case of March Networks’ remote-monitoring service, trained professionals in our Ottawa-based Network Operations Center (NOC) proactively monitor the health of our customers’ surveillance network and perform remote troubleshooting and issue resolution as part of our Insight Monitoring and Resolution Service. To do so, the NOC requires remote access to our customer’s on-premise server installed with March Networks Command™ Enterprise Software (CES) to monitor all registered hardware. Typically, most users provided remote access via a traditional VPN connection; however, there is an alternative that offers the same level of security with enhanced functionality.
That alternative is called SecureLink. It works by having a software agent (the SecureLink Gatekeeper) installed on the CES within the user’s network. The Gatekeeper automatically connects, using outbound https, to a SecureLink appliance residing within March Networks’ secured environment. Through the customer’s account on the appliance, he or she has full control of the NOC’s remote access, choosing between 24/7, scheduled, or on-demand access. The customer can also review an MP4 video of the NOC’s remote-access session for auditing purposes. The credentials to the Windows CES Server are gained through a customer-managed password control or “credentials vault” and passed on to the Gatekeeper without the requirement for the customer to divulge those credentials to the NOC.
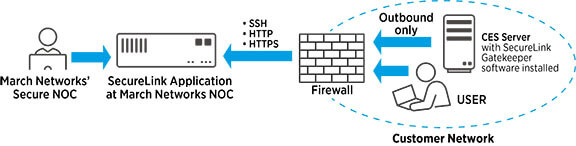
This type of remote-access control includes mechanisms to reduce risk and increase visibility when it comes to user-access rights. As a remote-access solution, SecureLink secures the greatest point of risk in working with third parties – the point of connectivity. This method of remote access verifies each user with multi-factor authentication (MFA), deploys fine-grained access controls like access notifications and scheduling capabilities, and provides zero-trust network access (ZTNA), which grants the least amount of access possible that allows a third party to perform its job, with access defined down to the host and port level. For customers who choose this option for March Networks’ remote-monitoring services, they can log in to see who is accessing their networks, when and why they are, who approved the remote access, and exactly what was done while their networks were accessed remotely.
While granting remote access via VPN has much to offer in terms of privacy and cybersecurity and remains a good option for many, having an alternative method of doing so is an added bonus for others. As compared to a provider setting up a VPN connection, which can sometimes take weeks depending on the scale of the organization, once approved, SecureLink usually takes just minutes to connect and be ready to use.
A remote monitoring solution for your video system lets organizations leave the health and maintenance of their surveillance infrastructure in the hands of an experienced team of trained professionals, which can help drive productivity and accountability and let all parties operate smarter. And with the additional secured remote-access option now available when you choose a March Networks solution, you can opt for the method of remote connection that works best for your business and relax knowing your data is secure.